First released in 2007, Open Authorization (known as OAuth for short) has become a staple authorization protocol on many websites, applications, and even mobile devices—especially for developers who wish to collaborate with other organizations.
We all know the cardinal rule to never share your password—and that’s never been more true! Despite their popularity, passwords aren’t as secure as we once believed. In fact, around 90% of user-generated passwords are vulnerable to hacking due to weak, user-generated credentials.
Thus, OAuth is an important piece of any organization’s website authentication because it protects users’ credentials. However, there tends to be a lot of confusion surrounding this particular method and how it actually works.
If your website requires a login to access particular information (such as a social media profile, online banking account, or eCommerce site), understanding how OAuth works is crucial. By using it in your website authentication process, you can simultaneously improve your user experience and secure sensitive user data.
That’s why we’ve put together this comprehensive guide to help you get a better understanding of OAuth— and how to implement it for your own authentication process. Let’s walk through the following commonly asked questions concerning Open Authorization:
- What is OAuth?
- What is OAuth used for?
- How does OAuth work?
- Why is OAuth popular?
- How secure is OAuth?
- What can I improve security with OAuth?
A lot of topics discussed in this guide require some basic knowledge of security authentication and authorization (and the key differences between the two). Before jumping in, you might want to use our comprehensive guide to brush up on the topics. Otherwise, let’s get started?
Say Goodbye to Passwords
and
Hello to Secure Logins.
Go passwordless and delight your users with secure and seamless one-click login.
1. What is OAuth?
Open authorization (or OAuth for short) is a type of token-based authentication that allows organizations to share information across third-party services without exposing their users’ usernames and/or passwords. Essentially, OAuth is the middle-man that provides third-party services with a token that allows only specific account information to be shared.
In other words, OAuth is a process in which users grant websites or applications access to information on another website without providing their login credentials. Then, OAuth ensures that the website requesting the information has the right permissions to access the user’s data.
What is OAuth 2.0?
OAuth 2.0 is a 2012 rewrite of the original Open Authorization protocol that provides a more comprehensive solution for modern web and non-web clients alike. OAuth 2.0 is the current industry standard framework for authorization software.
Nowadays, when you hear the term “OAuth” it will typically refer to OAuth 2.0 rather than the original protocol. As we walk through the rest of this guide, bear in mind that we, too, are discussing the current industry standard protocol of OAuth 2.0.
2. What is OAuth used for?
You’ve probably used OAuth without even realizing it. For example, whenever you give a website permission to access your Facebook information, you’re using open authorization. This protocol is useful because it allows you to share a limited amount of information with the third-party site, rather than give them full control over your account with your login credentials.
A common misconception about OAuth is that this process also verifies the user’s identity, otherwise known as authentication. As a result, OAuth often gets confused with single-sign-on (SSO) authentication. While the two processes are very similar and even share some basic characteristics, they have one key distinction: SSO authenticates users whereas OAuth authorizes users.
To better understand the difference, let’s first break down what authentication and authorization mean:
- Authentication is the act of verifying a user’s identity. When a user enters their username and password (or uses a passwordless credential), the website uses this information to confirm that the person is the intended user by comparing it against a secure database of user credentials.
- Authorization, on the other hand, occurs after a user has been authenticated. This is when the system checks to see what permissions the user has. A user’s permissions dictate what the person sees and what actions they can take on the website once you’ve confirmed that they are who they say they are.
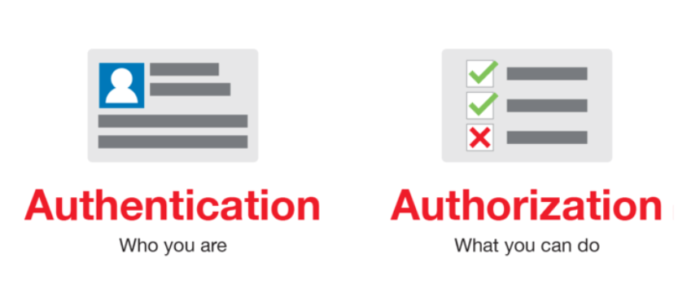
The simplest way to compare and contrast the two terms is as follows: Authentication asks the user, “who are you?” while authorization asks, “what are you allowed to do?” Thus, there is no authorization without authentication. However, mere authentication is not enough to secure accounts and provide specific permissions, thus the two processes work hand-in-hand.
OAuth serves the purpose of making sure that third-party websites have the right permissions to access a user’s information once their identity has been verified using a method of authentication.
3. How does OAuth work?
If you know a thing or two about token-based authentication, then OAuth is pretty simple to understand. The process in which a website obtains a token is called a flow, and in the OAuth flow, there are three key players: the user, the consumer, and the service provider.
To better explain how this process works, let’s imagine that your organization (the user) wants to use a social media management tool to schedule and publish your Facebook posts. In this example, Facebook is the service provider, and the social media management tool is the consumer of the data being requested.
Here’s how the OAuth process would work:
- The user requests an action. In this initial step, you’ll let the social media management tool know that you want to automatically publish posts using their service.
- The consumer gets permission from the service provider. The social media management tool will ask Facebook to grant it permission to access your account and publish posts. In return, Facebook will send them a token with a unique signature or secret code that verifies the management tool’s actions.
- The user is redirected to the service provider. Once the social media management tool has the token, it will redirect you to Facebook’s login page.
- The user gives the consumer permission. When you’re redirected to Facebook’s login page, it will ask for your username and password and to confirm that you want the social media management tool to be able to post on your behalf. Once permission has been granted, the token will be approved and used every time the social media management tool makes a request.
- The consumer accesses protected permissions. Now that the social media management tool has the token, it is able to complete tasks because the token delegates which permissions it has access to.
It’s important to note that never in this interaction did you have to give your login credentials to the social media management tool. Instead, the token acts as a placeholder, which also ensures that the consumer (or the third-party application) never has total access to your account.
For example, if the social media management tool made a request to change your Facebook account settings, this action will be denied because the token only states that the consumer has permission to post on your behalf.

1-Click Login is a simple & secure password-free authentication service.
With our patented technology, your website can improve security & increase customer conversion by removing passwords.
4. Why is OAuth popular?
In order to understand why OAuth is so popular, we have to look at how information was shared before its existence. If a user wanted to share information from one account to another, the individual had to give their credentials to the third-party website. As a result, many not-so-credible websites were taking advantage of this weakness and using a person’s credentials to obtain sensitive information.
Additionally, this outdated process doesn’t restrict what actions another website can do. With your username and password, the third-party website could:
- Make changes to your settings
- Access sensitive information like a credit card number
- Change your credentials and block your access to the account
OAuth originated as a process that didn’t share credentials and dictated what a website had the ability to do. Having a secure way to share information across different websites means that companies and applications can collaborate more often and provide more convenient and streamlined services for their users.
OAuth not only makes it easier for the third-party website to gain the information they need, but it also makes the process more convenient for the user. OAuth is a popular solution for both websites and users because it’s more secure than sharing credentials and allows users to utilize services across multiple platforms.
5. How secure is OAuth?
Since OAuth doesn’t share your credentials with other websites, it’s more secure than the alternative method mentioned above (providing your login credentials to a third-party website). However, it’s important to be aware that OAuth has its own weaknesses— one of the most crucial occurring at the step when users are redirected to the service provider’s website to enter their credentials.
Let’s go back to our example in the second section:
If the social media management tool that requested access to your Facebook data turned out to be a malicious website, it might direct users to a site that looks just like Facebook but actually isn’t. When you log in, the malicious website will process and store your username and password. That’s why it’s always important to make sure that you’re being directed to the correct website when you grant the consumer access.
Additionally, without the right specifications, OAuth tokens don’t expire. As a result, these tokens are vulnerable to attacks. If a hacker gains access to a token or the secret that verifies the token, they would be able to trick the system into making unauthorized requests.
Because hackers are smart and constantly discovering new ways to gain access to users’ credentials and personal accounts, there is no authentication or authorization method that is completely foolproof. However, that doesn’t mean that all passwordless or token-based methods aren’t secure. Just as cybercriminal technology is evolving, so is ours. That just means that you, as the developer or web designer, have to stay up-to-date on new and developing practices to minimize the risk for you and your users.
6. How can I improve security with OAuth?
Many other token-based methods like email authentication provide users with a secure way to verify the user’s identity without as much risk. Let’s say you wanted users to be able to log into their accounts without a username or password.
Email authentication allows users to complete the login process using their personal email account, thus strengthening security and reducing the need to remember another set of credentials.
Here’s how Swoop’s Magic Message™ email authentication process works:
- The user is redirected to the Swoop service via the OAuth 2.0 protocol for authentication.
- From a browser window, the user pushes the “Send Magic Message” button: The button activates a mailto link, which generates a pre-written email for the user to send.
- The user sends the email: This is where the magic happens. Once the email is sent, the outgoing email server generates and embeds a 1024/2048 bit, fully encrypted digital key into the header of the email. Swoop’s authentication server follows the public key cryptographic procedure to decrypt this key. Each email sent receives a unique key for that message. The level of security for these encrypted keys is beyond comparison to traditional passwords.
- The user is logged into their account: When the key decrypts and passes all layers of verification, the Swoop authentication server directs the website to open the user’s account and begin a session. This all takes place in a matter of seconds and makes for an extremely streamlined user experience.
Swoop’s magic email authentication system has been made possible by building in conjunction with OAuth’s uber-secure authorization protocol. It’s also more user-friendly than a traditional password-based system because it’s one less set of credentials for a user to remember in the first place!
Now that you’re familiar with the ins and outs of OAuth, you’re ready to improve your website security and user experience. For more information about website authentication and security protocols, check out these additional resources:
- Password Authentication: Avoiding 4 Common Vulnerabilities. Interested in learning more about the weaknesses of passwords and how they could be affecting your website’s security? Keep reading this article to find out more.
- Top 3 Password Alternatives For Better Website Security. We briefly mentioned how password alternatives can boost web security and user experience. Learn more about our three favorite password-free login methods with this guide.
- User Authentication: Understanding the Basics & Top Tips. As you might have guessed, OAuth is part of a much larger discussion on user and website authentication. Get an in-depth understanding of user authentication with this article.