There’s no greater annoyance than being unable to log in to a website due to a forgotten password. It’s so frustrating to sit there guessing at your password and getting it wrong over and over. What if you’re ultimately unable to access your account and complete the (probably very simple and quick) task you were trying to complete?
However, the real problem is that passwords cause serious security vulnerabilities for users, developers, websites, and applications. In fact, security experts claim that approximately 90% of passwords are hackable due to weak, user-generated, and recycled credentials.
That means a human-generated password will be predictable 9 out of 10 times, and hackers can easily access the information they need to crack weak passwords using social engineering techniques and/or brute-force attacks.
This doesn’t just apply to personal accounts, either. Password security issues can seriously derail a company’s website. Luckily, technology has progressed past the need for passwords thanks to innovative password-free solutions.
What is a password?
Before we jump into top password alternatives, it’s important to establish exactly what a password is— and what it isn’t. A password is a unique string of characters used for identification purposes on websites, applications, mobile devices, and more.
Essentially, when a user creates an account, they choose a unique ID and key (typically a username and password) that will be used to verify their identity upon login going forward. Ideally, the user is the only one who knows this ID and key, thus proving they are who they say they are when they request reaccess.
However, it’s important to note that although they’re still the most widely used, passwords are not the most secure or reliable form of user authentication.
What are the main drawbacks of passwords?
In short, passwords have the following significant drawbacks:
- They’re easy to forget.
- They’re difficult to manage across a variety of systems.
- They’re easily susceptible to major hacks.
- They frustrate users and hinder growth for websites.
All things considered, passwords are a major problem, and the internet would be so much better if there were a way to get rid of them.
Luckily, there is— and that’s where password alternatives come in.
Not only are these alternatives more convenient but they also enforce stronger security policies to protect you and your users’ personal information. Follow along as we explore the following password alternatives that more and more organizations are taking advantage of:
By the end of this post, you’ll better understand that you simply don’t need to force your users to create passwords on your site. By getting rid of the barriers that passwords create, your website can grow and prosper. Ready to get started? Let’s jump in!

1-Click Login is a simple & secure password-free authentication service.
With our patented technology, your website can improve security & increase customer conversion by removing passwords.
Password Alternative #1: Email Authentication
Email has long been one of the most important of all online accounts. In fact, our personal email accounts typically act as a sort of hub for every other account we create online. We use it to reset forgotten passwords on other sites, for instance.
The central position of email to all your digital accounts means that if your email account gets compromised, everything else could be at risk. All the modern email providers, including Gmail, Yahoo, and Outlook, provide advanced security features such as 2FA (Psst…turn it on if you haven’t already) that you can easily turn on to lock down this most important account.
Password alternatives and techniques that build on this level of security can provide some of the fastest, most effective, and safest log in experiences available.
In fact, some sites have been doing it for quite some time now when onboarding a user to generate a password. The most common way of leveraging email account security to authenticate web users involves what is known as the “Confirmation Email” where the user opens a confirmation link. Swoop’s Magic Link™ takes this one step further as a way to replace the password altogether.
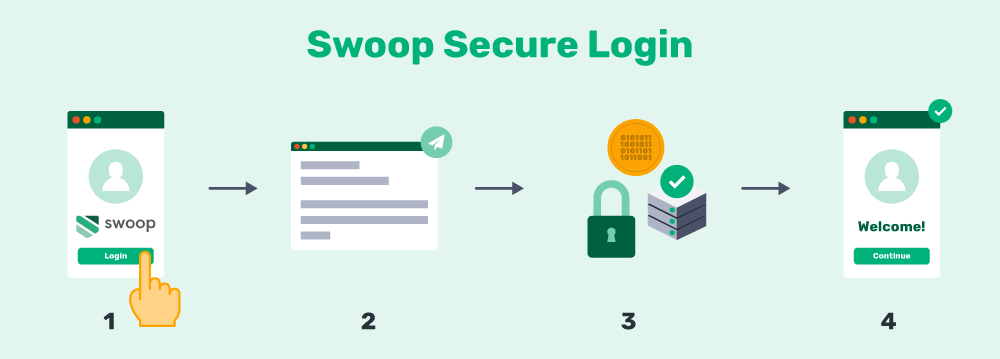
- User clicks a “Login with Swoop” button.
- Swoop sends an email to the user with a unique and highly secure Magic Link™.
- The user clicks the link from their email client, which verifies their identity.
- The user is granted access to the secondary account.
Magic Links™ are highly efficient and effective for removing the need for passwords, and they offer more advanced security. Magic Link™ offers a simplistic, frictionless freedom when authenticating a user for a website or application. This experience becomes even more magical after the first authentication process by offering a 1-click login option from that point forward.
However, email authentication systems have not stopped there. The magic has evolved to produce an even simpler, more secure process known as the Magic Message™.
Combining the Magic Link™ authentication system described above with innovative security procedures results in a faster, even more user-friendly log in experience that completely removes the need for passwords. Here’s how it works:
Step #1: The user is redirected to the Swoop service via the OAuth2 protocol for authentication. From a browser window, the user pushes the “Send Magic Message™” button: The button activates a mailto link, which generates a pre-written email for the user to send.
Step #2: The user sends the email: This is where the magic happens. Once the email is sent, the outgoing email server generates and embeds a 1024/2048 bit, fully encrypted digital key into the header of the email. Swoop’s authentication server follows the public key cryptographic procedure to decrypt this key. Each email sent receives a unique key for that message. The level of security for these encrypted keys is beyond comparison to traditional passwords.
Step #3: User is logged into their account: When the key decrypts and passes all layers of verification, the Swoop authentication server directs the website to open the user’s account and begin a session. This all takes place in a matter of seconds and makes for an extremely streamlined user experience.
By leveraging email accounts and magic authentication products like Magic Link™ and Magic Message™, sites have the option to completely and literally eliminate passwords from that domain. Plus, practically everyone online has an email account, making this a truly universal solution to eliminate the password.
Authenticating through a digital key is a simple and cost-effective choice. No special biometric hardware required, no app to download, and no customer opt-in needed. One simple integration and you’re in business. Your users are free to log in to a discussion, see premium content, or make payments without the stress or hassle of passwords.
How Does Swoop Protect Sensitive Information?
This is the chief concern of many companies that need to handle sensitive personal and financial data. The good news? Swoop’s authentication method does not expose sensitive information.
The only possible vulnerability in the process occurs during the transmission of the email to the authentication server. However, Swoop tokenizes all the details about the authentication (i.e., the site being logged into or the type of account being set up), making them indiscernible to third parties.
How does Swoop confirm an email account is valid and not spoofed?
The digital keys embedded by the outgoing mail server prevent the authentication server from being spoofed. Using the public key published in the DNS registry to decrypt the digital key, then confirming the match, provides an unparalleled level of security. This is called the Domain Key Identified Mail system, or DKIM.
DKIM is already used by all major email senders to prevent spoofing, but Swoop also makes use of the Sender Policy Framework system, or SPF, to track the progress of each authentication. SPF checks to see that the email traveled from authorized server to authorized server.
The bottom line: Swoop’s password- free email authentication is an exciting option for completely eliminating passwords from your website.
No other technology, by itself, offers this same opportunity or can take your website into the future of security and user experience. The future of the open internet is password-free, and Magic Link™ and Magic Message™ authentication is the best way to get there.

1-Click Login is a simple & secure password-free authentication service.
With our patented technology, your website can improve security & increase customer conversion by removing passwords.
Password Alternative #2: Social Media Authentication
Here’s another of our favorite password alternatives. As a step down from password-free magic authentication, social media login options are still a strong choice for sites that want to eliminate the need for new users to create passwords.
They work on a similar concept, too. Building from the more advanced security features embedded in the authentication processes of top social media platforms, these solutions offer another user-friendly way to log in fast without using a password. Instead, users log in to your site via Facebook or Twitter, effectively acting as a secure proxy validation.
Pros of Social Media Authentication
As a password alternative, social media account authentication has a few major benefits, including:
- The ability to significantly reduce the need to create new passwords
- Tons of saved storage space across the internet
- Significant increases in account creation on your site by streamlining the process of data input
Overall, utilizing a social media account to log in to a third-party website or application is a great way to speed up the registration process and provide a user-friendly alternative to traditional passwords.
Cons of Social Media Authentication
There are a few downsides to social media login options, though. Many web users are uncomfortable with linking their social media profiles across their other accounts. Plus, many consumers simply don’t trust the social media giants following recent scandals of unethical data practices. A Pew Institute study recently found that 60% of Americans won’t use social media account authentication options.
Offering a few social media account authentication options most relevant to your users in addition to a universal email authentication option will create a truly comprehensive set of password alternatives.
Password Alternative #3: Biometric Authentication
The last of our favorite password alternatives— biometric authentication— involves some developing technologies. Biometric systems use our unique biology to replace the need for a password.
A common example? Many of us already use fingerprint scanners on our smartphones to avoid manually entering a code every time we want to unlock them.
That’s why using biometrics to log into an account or make payments is a natural next step for this digital security system. Biometric systems rely on an additional security element that’s personalized to each user. This highly customized process helps users access accounts or make online payments with just one step.
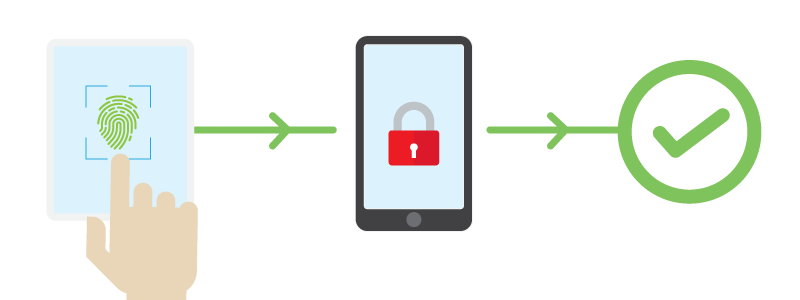
For instance, the fingerprint payment system requires users to have a device with finger scanning capabilities. While the process varies slightly from one device to the next, the primary steps are the same:
- The user just needs to rest his or her thumb or finger on the device’s scanner.
- Unique patterns from the fingerprint are compared against those stored in the device’s secure database.
- Once the user’s thumbprint is confirmed, the individual can access his or her phone and make online payments.
Biometric scanners are also now being used to make online payments, such as Mastercard’s fingerprint and facial recognition technology which confirms a cardholder’s identity for easier online shopping. With the steady influx of biometric verification, companies can only imagine how these tech initiatives of tomorrow can impact security issues today.
Pros of Biometric Authentication
There’s no denying that biometric authentication is more glamorous than traditional passwords, and thus more appealing. After all, everyone has a totally unique set of biological features; it only makes sense for us to use these password alternatives as a way to enhance both on- and offline security.
Other significant merits of biometric authentication include:
- Fingerprints and iris scans are harder to fake than payment or identity cards.
- The key to accessing your account or making payments is always with you and can’t be forgotten.
Thanks to the ease-of-use for the end user, biometric authentication has become increasingly popular in the last few years. But is it the best passwordless alternative? Not so fast!
Cons of Biometric Authentication
Despite its high-tech allure, there are a number of disadvantages to take into consideration with biometric systems. Consider these drawbacks:
- Accessing a device that can scan your fingerprints or face can be costly.
- Someone can copy your fingerprint or eye retina to create a replica.
- Scanners can be fooled by a picture/mold of someone’s fingerprint or a contact lens of someone’s eye retina.
- Someone can force you to use your fingerprint to unlock confidential information.
It might seem that many of these potential issues involve extreme dedication and expertise. While some certainly do, recent developments have begun to indicate that the fingerprint sensor on your phone is not as safe as you think!
Smartphone fingerprint scanners are a great example of the inherent weaknesses of biometric login systems. Smartphone fingerprint scanners are small, so the phone records multiple partial images of your fingerprint. A swipe only needs to match one to gain access. One biometrics expert estimates it would be extremely easy to gain access to 1 out of 10 phones with biometric login enabled. The limitations of the technology makes biometrics a surprisingly vulnerable authentication method for many contexts.
However, this solution is also developing extremely quickly. Where there are vulnerabilities today, they may be eradicated in the near future. As a result, we’ll likely see a truly secure and effortless biometric authentication option within the next several years.
Say Goodbye to Passwords
and
Hello to Secure Logins.
Go passwordless and delight your users with secure and seamless one-click login.
Passwords need to go. There are real, powerful alternatives out there that can help get rid of them once and for all, ready to be adopted whenever you’re ready to get on board. We believe the future of the internet relies on a combination of these three password alternatives.
For more information on password security and website authentication, take a look at our additional resources:
- 6 Shocking Reasons Why Passwords Won’t Protect Your Website — Still not convinced that password alternatives are the best option for your organization? Our article addresses six main reasons why using passwords could put your organization’s information at risk.
- Understanding the Fundamentals of Website Authentication — Want to learn more about how users can verify their accounts? Our comprehensive guide is full of tips and tricks to improve your website’s authentication.
- Single Sign-On Authentication: The Swoop Guide — SSO authentication is an extremely important step in the process of eliminating passwords! Learn about the process, benefits, and limitations of this method with our handy guide.