Fingerprint scanning (a type of biometric authentication) has become a popular password replacement in recent years. In fact, fingerprint scanning is used in many smartphones as a way to unlock the home screen and authorize online transactions.
The user enjoys a quick and easy process and doesn’t have to deal with the inconvenience of creating or remembering a password. Plus, fingerprint scanning is more secure than a password because our unique biological characteristics can’t be cracked or easily duplicated.
As a result, you might be considering this option to provide an easier login experience for your user.
However, before you start implementing this tool on your website, it’s important to fully understand this passwordless authentication method to determine if it’s the right option for your organization.
To help you with the decision-making process, we’ve compiled a list of 5 essential areas you should understand about fingerprint scanning:
- History of fingerprint scanning
- The fingerprint scanning authentication process
- Ways fingerprint scanning can be used
- Advantages of using fingerprint scanning
- Weaknesses of fingerprint scanning authentication
If you’re new to website authentication or how the user login process normally works, we recommend checking out this guide to brush up on the basics.
Now, let’s dive into the ins and outs of fingerprint scanning!
1. History of Fingerprint Scanning
While you might think of fingerprint scanning as a new development spearheaded by Apple with their touch to unlock home button, the truth is that fingerprint scanning has been around for quite some time.
In fact, the idea of biometrics—using one’s biological characteristics as a form of identification—dates back as far as 31,000 years ago when it was believed that prehistoric men marked caves with handprints as a type of signature.
Since 1858, fingerprints have been used as a way to verify signatures and more recently as a form of identification for the FBI and police departments.
Until 1975, all fingerprint identification was completed manually. The FBI funded the development of automated scanners and with the help of NIST (National Institute of Standards and Technology) focused on creating digital images of fingerprints and testing the effects of image quality on the identification process.
Law enforcement has used fingerprint scanning for more than a century, perfecting the process and the technology that followed.
But it wasn’t until about a decade ago that fingerprint scanners became a viable option for consumers. The reason why we remember Apple’s Touch ID feature so much is because it was one of the first times this technology was implemented in a reliable and user-friendly way.
Now there are over 180 phones with fingerprint scanners, and biometrics appears to be an authentication method that’s here to stay.
In summary: Fingerprint scanning has been around for a long time, perfecting the process, and has only just become more accessible to a wider range of users.
Say Goodbye to Passwords
and
Hello to Secure Logins.
Go passwordless and delight your users with secure and seamless one-click login.
2. The Fingerprint Scanning Authentication Process
Whether you’re a corporation or nonprofit that’s looking to implement fingerprint scanning, it’s important to know how the process works for your users and what’s going on behind the scenes.
The User’s Experience
The process is very simple on the user’s part. Here is how the process works:

If a user wants to unlock his phone, he just has to put his finger on the phone’s fingerprint scanner and wait a couple of seconds for the device to grant him access.
The fingerprint scanner has two jobs: capture an image of the print being scanned and confirm that the pattern matches the one on file.
As a result, users have to also set up fingerprint authentication before it will work. In order to do this, users must first let the device complete an initial scan of their fingerprint, which is used as the image for comparison.
Keep in mind that every fingerprint is different, so whichever finger the user decides to scan will be the only finger that will grant them access. Many devices, however, do allow users to keep multiple fingerprints on file.
The Technical Side of Fingerprint Authentication
So how does the device determine a match?
The system will only compare the two fingerprints focusing on the minutiae, unique characteristics in your fingerprint where the ridges end or split in two.
When users complete the initial scan of their fingerprint the system pinpoints the minutiae and transforms the information into an encrypted key or mathematical code.

This code is what the system actually stores for comparison. Since the code can’t be reconverted back into the image, the system can securely store in information so that it can’t be used by a hacker.
When the user wants to unlock their phone screen, he’ll place his finger on the scanner. The system will scan the fingerprint and transform it into a code and compare that code with the original.
To confirm a match, the two prints don’t have to be exactly the same. If the two prints have a sufficient number (determined by the scanning system) of minutiae in common, the system will authorize the request.
In summary: The fingerprint scanning process transforms prints into a unique code that is then compared to the original print scanned in order to confirm a match.
3. Ways Fingerprint Scanning can be Used
As we’ve mentioned above, fingerprint scanning is used by law enforcement as a form of identification. Additionally, with the implementation of fingerprint scanners on phones, it can be used to unlock a device and authorize payments.
When it comes to your organization, you probably have a few ideas of how you’d like to use fingerprint scanning, but there are several ways you can utilize this authentication method, including:
- Authorization into buildings or restricted areas: Much like how Apple uses fingerprint scanning to unlock a device, companies can use fingerprint scanning to unlock doors to keep access restricted to only those that need it. Since keys can easily be duplicated or compromised like a password, using fingerprint scanning acts as a way to make their buildings more secure.
- Building security procedures: Banks often use fingerprint scanning as another form identification when an employee enters the building as a way to record who is in the building at all times.
- User login (replacing passwords): Fingerprint scanning can be used to replace any traditional login process that requires a username and password. For instance, many smartphone applications allow users to sign on using fingerprints as their credentials.
- Confirm online payments and donations: Additionally, with logins replaced by fingerprint scanning, this means that users can also confirm transactions using fingerprint scanning. If your users’ credit card information is on file, they can simply scan their fingers to make a purchase or donation.
Fingerprint scanning can be used in several situations when identification is required to complete a task or when identification allows your company to be more secure in your day-to-day operations.
In summary: Fingerprint scanning can be used in a variety of situations to make processes more secure and convenient for your users.
4. Advantages of Using Fingerprint Scanning
With more technology developing, it has become easier for cybercriminals to gain access to our information by cracking passwords and breaching user databases. Coupled with the fact that people store more sensitive data online than ever before, it’s important that we accept the weaknesses of passwords and look to other solutions.
Fingerprint scanning offers a more secure alternative because it relies on information that can’t easily be stolen or replicated.
Moreover, it eliminates many inconveniences that traditional login systems possess. For instance, fingerprint scanning removes the:
- Need to create a string of characters, numbers, and symbols as a password.
- Process that requires users to remember a different set of credentials for each device, website, or computer program.
- Ability for unauthorized hackers to guess or crack your credentials.
Since there is nothing to remember or carry with you, fingerprint scanning isn’t a hassle for the user.
Additionally, the process can be completed in a matter of seconds. With a traditional login process, the user has to type in their username and password. If users are following updated password security guidelines, their passwords may be as long as 16 characters with no logical order to the symbols, letters, or numbers used.
As a result, this would take more time and effort to enter than placing their fingers on the scanner and waiting for the device to confirm their identity.
In summary: Fingerprint scanning is not only more secure than passwords, but it’s also less time-consuming and easier to manage.

1-Click Login is a simple & secure password-free authentication service.
With our patented technology, your website can improve security & increase customer conversion by removing passwords.
5. Weaknesses of Fingerprint Scanning
Before you can finalize your decision, you should be aware of the weaknesses associated with fingerprint scanning and potential solutions that might better fit your organization’s needs.
One of the biggest drawbacks with fingerprint scanning is that these systems can be tricked by an image or mold. Of course, this requires the hacker to obtain a copy of the user’s fingerprint, which is relatively difficult to achieve and more work than most cybercriminals are willing to do.
Unfortunately, creating a copy of the user’s fingerprints isn’t the only way an unauthorized user can hack the system. In a recent study, it revealed that fingerprint scanning systems can be fooled by a master fingerprint that is composed of many common fingerprint characteristics.
As we mentioned earlier, fingerprint scanners don’t need an exact match—just enough similar characteristics to approve the print.
As a result, cybercriminals are playing on this weakness by creating digitally composed prints with enough universal similarities to trick the system into thinking there is a match 65% of the time.
Another concern with fingerprint authentication is that once someone obtains your fingerprints (or can trick the system into thinking it has your fingerprint), you can’t change them like you would a normal password.
You wouldn’t be able to use your fingerprints as a secure method of authentication ever again unless you knew that all copies were destroyed.
Aside from its gaps in security, organizations should also be aware that fingerprint scanning can be costly to implement. Even once it’s implemented, without a device that can scan fingerprints, users won’t be able to use this feature.
Despite the number of phones currently using fingerprint scanning, it isn’t a feature that’s accessible to everyone and will cost the user an additional expense to obtain a device with this capability.
Fingerprint Scanning Alternatives
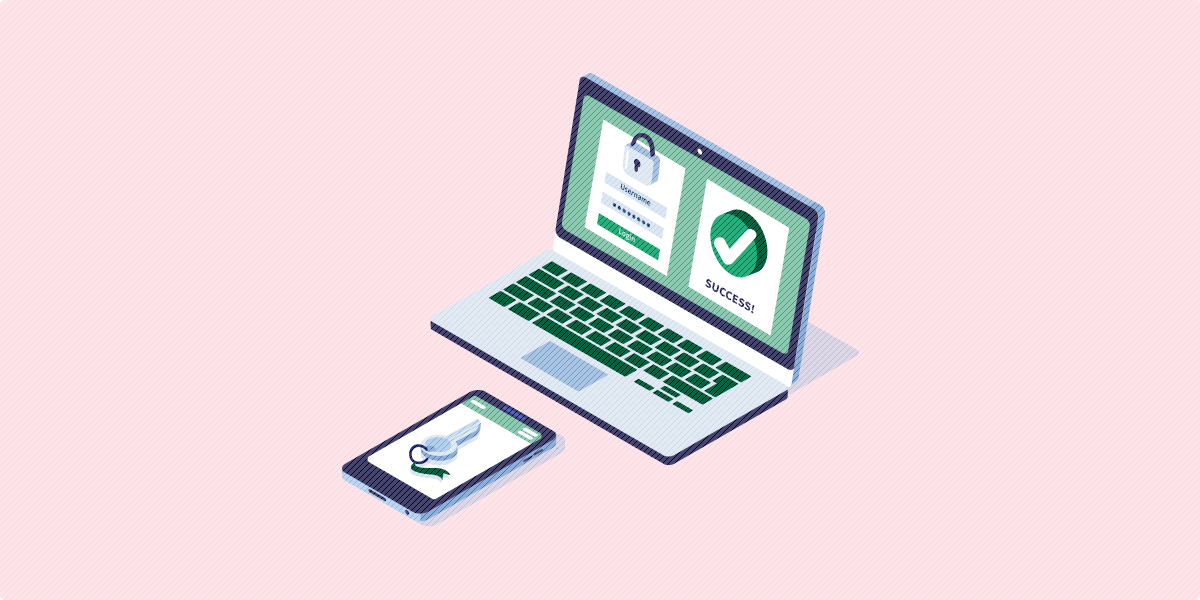
With these weaknesses, you might have second thoughts about using fingerprint scanning. Another alternative that doesn’t require users to have a password is email authentication. This authentication method can be used by anyone with an email address and can be completed in two simple steps.
Here is how Swoop’s email authentication process works:
- Users just need to click on the “Sign In” or “Pay Now” button, which will trigger a mailto link. This link will direct them to a pre-written email with more information on the requested action.
- Once users end the email, all they have to do is wait for a few seconds before their transactions are confirmed or they’re able to enter their accounts.
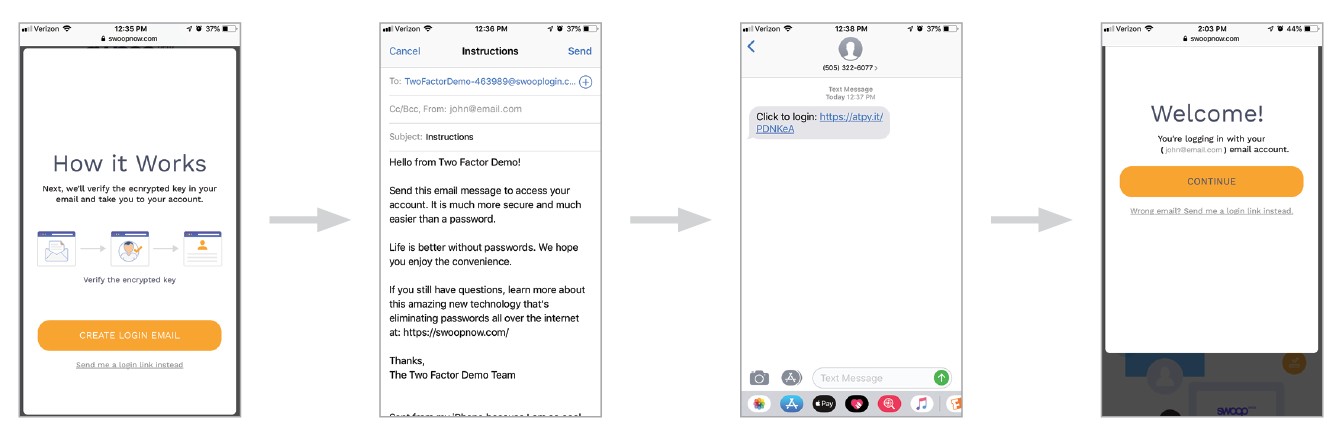
Each email has a special code attached to the message that identifies the user, so if the system doesn’t recognize the device or IP address used, the system will send you a message via text message so you can confirm or decline the request.
Best of all, email authentication can be used to log into accounts, sign up for subscriptions, make online purchases, or donate to a nonprofit organization.
In summary: While fingerprint scanning has many advantages, its security and accessibility weakness can be a serious concern for many organizations. That’s why looking into alternative options like email authentication might be a better password alternative.
Now that you understand how fingerprint scanning works and the many advantages and challenges with this authentication method, you can decide if it’s the right option for your organization.
If you’re interested in researching other passwordless options, check out these additional resources:
- Why Passwords Won’t Protect Your Website: Looking for more reasons why you should switch to a passwordless login system? Check out these 6 shocking reasons passwords don’t offer good security.
- What is SSO Authentication Work & How Does It Work?: Learn more about other types of authentication by starting with SSO authentication. This is a great way to improve the login process when your organization has multiple domains.
- Understanding User Authentication: 3 Basics You Should Know: If you’re curious how user authentication works, this guide provides an in-depth look and offers ways to improve your website’s user experience.