If your company or organization is looking into passwordless login options, you’ve probably heard a lot about authentication APIs and implementing them into your company’s existing infrastructure. To put it simply, an API gives your company the tools you need to implement the desired passwordless security option, but we’ll dive deeper into that in the first section.
When considering a passwordless login vendor, it’s important to understand what features are included in their API and how information is securely transferred between the vendor and your application.
Entering the world of authentication application programming interfaces (or APIs for short) can seem like a daunting task. That’s why we’ve created our complete guide on APIs to help your company understand all the components that make up a top-notch system.
Here’s what we’ll cover:
- What is authentication API and why does your company need to use it?
- What features should developers look for in a reputable authentication API?
- What should developers expect during the authentication API integration process?
We’ll answer your questions about authentication process and advise you on what to look for when choosing a passwordless login vendor. Let’s get started!
1. What Is Authentication API and Why Does Your Company Need to Use It?
Essentially, an API is an intermediary software that allows two applications to talk to each other.
Any time you use an application such as checking the weather on your smartphone, you’re using an API. APIs allow applications to send information to your server, process the information, and perform the necessary actions.
An authentication API helps organizations implement a system that confirms their users’ identities, and the more complex (and secure!) the authentication process is, the more likely a company will need to implement an API.
With passwordless authentication options, the level of security that goes into verifying each user requires a lot of unique algorithms and barriers to ensure that no hackers slip through the cracks. When a user signs into an account with Swoop’s email authentication process, they only have to complete two steps, but there are several security checks that are going on behind the scenes:
- First, the email is authenticated using a DKIM signature. Every email has a DomainKey Identified Mail (DKIM) signature attached to it that is used by all email domains to detect email spoofing. Recipients can verify that the message was authorized by the user by looking up the sender’s public key in the Domain Name System. We check the DKIM signature to identify if the message came from the user.
- Second, the email is verified using Sender Policy Framework. Similar to DKIM, Sender Policy Framework (SPF) uses a path-based verification process where the sender is verified every time it passes through the email domain server. Once we receive the email, our system verifies that the path follows the correct domain server.
- Finally, our system conducts another layer of security checks based on our unique algorithms. Based off the information gained from the first two checks, our system goes through a third check to determine whether or not the request should be approved, rejected, or sent back for further confirmation.
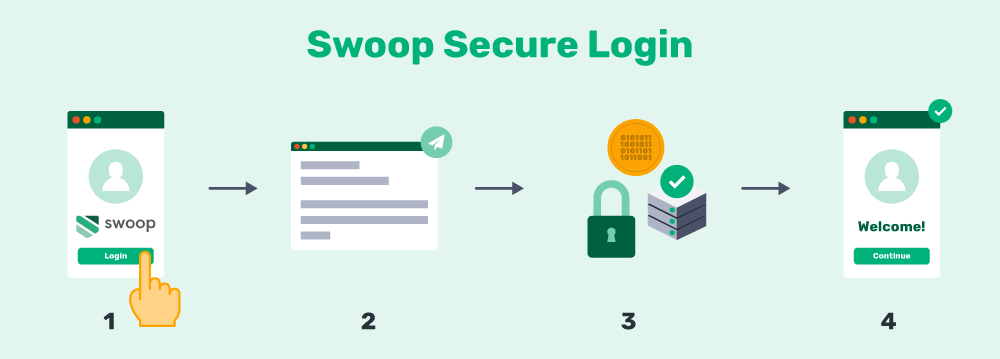
As you can see, a lot goes into the process. While Swoop does perform an extensive list of checks (better safe than sorry!), implementing a similar process on your own is a lot of work for your developers. Instead of you directly developing these security measures, authentication API vendors allow you to access their technology and use it on your application or website.
Key takeaway: Authentication APIs handle all the hard work for your company and its developers. All you have to do is simply integrate the system with your existing software. Just be cautious of how the API transfers information (see the next section).
2.What Features Should Developers Look for in a Reputable Authentication API?
A Secure Authentication Process
Before you choose any authentication API vendor, it’s important to understand how information is transferred. Just like your users need to authenticate their identities before accessing your application, you need to verify your company before you can access the API. Once you’ve been authenticated, your application is able to communicate with the authentication API and start transferring data.
Authentication API vendors can use several different types of authentication methods, including:
- Basic authentication, which is the simplest authentication method. This requires the company to have an API key (similar to a username) and secret (similar to a password). While not required, basic authentication should only complete requests via HTTPS, a secure version of HTTP. This means that any communication between the browser, application or website, and API is encrypted.
- OAuth allows users to grant applications access to certain information from another account like Facebook. We’ve talked about the OAuth process in more detail, but it is one of the most secure ways to transfer data between third-party applications because it only gives an application access to specific information the user approves.
As a result, organizations need to look for an authentication API that transfers information in a secure way. While your API will need information about your users to complete security checks, you don’t want this information to fall into the wrong hands because of your API’s lax security practices.

1-Click Login is a simple & secure password-free authentication service.
With our patented technology, your website can improve security & increase customer conversion by removing passwords.
No Password Required or Existing Account
Since we’re talking about a specific type of API that will handle your application’s authentication process, it’s important to look for a vendor that is 100% passwordless. This means that your users won’t need an existing password or account in order for the process to work.
Many application allow users to log in with Facebook or Twitter. While users don’t have to create a new password, they still have to have one of these accounts active to log in through this method. Swoop, on the other hand, lets users log in with any email address which is much more universal than a social media account.
What’s more, the Facebook or Twitter users need to make passwords that are extremely secure to ensure that hackers can’t gain access, whereas Swoop’s system uses the security practices of email domains and their own security algorithms to maintain a high level of security for users.
Compatible with Mobile Devices
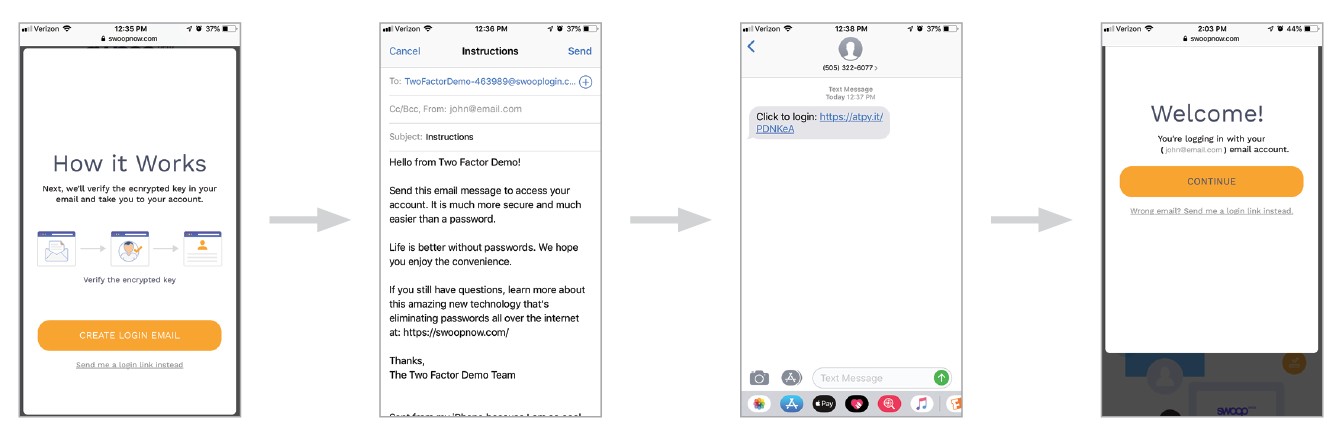
Another factor to keep in mind is that the authentication API you choose needs to be both flexible enough to accommodate all of your needs but also rigid enough to be secure and easy to use. A key component of that is whether or not the API is compatible with mobile devices and desktops.
Depending on your application, you might have users accessing your tools via a smartphone, tablet, or computer. No matter what device your users access and view the information on, the authentication API should be the same or have minor adjustments to better fit the device in use.
We may be a little biased, but Swoop is a great API because our login and sign up buttons were built for the speed and ease of use on a mobile phone, but that’s not to say that our tools won’t work on any device. Our login and signup buttons can be used on emails, mobile phones, websites, and so much more!
Easy Setup Process and Customer Support
Last, but certainly not least, you need to look for an authentication API that has an easy setup process. After all, the reason why you’re looking for an authentication API is to avoid creating the authentication code yourself.
Your authentication API vendor should:
- Provide API documents that describe the system’s authentication process and the code for the various features they provide.
- Support you through the process and assessment of your website’s infrastructure.
- Walk you through how the passwordless authentication process works for the user.
This last point is extremely important because your team needs to understand how the login process works. That way, they’re able to guide users through the process and troubleshoot minor challenges.
This is just a brief picture of what you should expect during the setup process (we’ll go into more detail about the setup in the next section).
Key takeaway: Every company will have different needs and expectations when it comes to finding an authentication API, but the four features — secure authentication, no passwords, mobile friendly, and easy setup — should be offered by any vendor you pick.
3. What Should Developers Expect During the Authentication API Integration Process?
When it comes to the integration and setup of your authentication API, it’s important for your developers to know what they’re getting into so that you can avoid the headaches that come with being unprepared. There are a lot of steps that go into the integration process, and everyone on your team and the vendor’s team needs to be on the same page.
Once you’re ready to purchase, here is how the process will likely go:
- Contact the vendor and/or set up an account that gives instant access to their API.
- Sometimes the API vendor will assess your current website’s infrastructure to determine how to best implement their API.
- You’ll gain access to the vendor’s API documentation that your developers can use to set up the system.
- The vendor will be available to provide any help or support if the authentication API isn’t working correctly.
Depending on the type of authentication API your company chooses, you might have different steps or parts in the setup process that are the vendor’s responsibility to complete. For instance, when setting up Swoop’s API, our developer team will create the mailto link with a unique token identifier. This email will be the address that all login requests are sent to and will appear in the “To” field in the user’s pre-written email.
Without this step, the email won’t be sent to the right system, and Swoop won’t be able to perform the security checks necessary to approve the request.
Say Goodbye to Passwords
and
Hello to Secure Logins.
Go passwordless and delight your users with secure and seamless one-click login.
No matter what authentication API vendor you choose, make sure that your developers understand all the steps that go into the implementation process as well as what steps need to be completed by the vendor.
With your new API set up, your team should also consider how you’re going to introduce the login system to your users. Its likely that the following systems are new to your customers and employees:
Work with your developer team to create a user onboarding plan that trains users on how to log in and use your application.
Key takeaway: Work with a vendor that will help guide you through the setup process and explain what’s needed from your developer team so that you can move through the setup as smoothly as possible.
Authentication APIs can be a great asset to your organization because they allow your company to offer users a convenient way to log in and set up an account. And, since there are no credentials, your users’ accounts stay protected. Hopefully, this guide has helped you understand authentication APIs and what to look for when choosing a vendor.
If you want more information on website authentication or passwordless login, check out our additional resources:
- Two-Factor Authentication: A Definitive Guide For Websites. If you’re not comfortable using passwordless login systems but still want to give your users’ accounts and added layer of protection, why not consider two-factor authentication? With two-factor authentication, your users will have to enter their password and another code sent to the phones or emails to access their accounts.
- 4 Password Authentication Vulnerabilities & How to Avoid Them. Many security experts are predicting the end of passwords because of the inconvenience and inability to successfully protect our accounts. Learn about all the risks password authentication presents as well as some ways to solve these challenges.
- Are Your Passwords Compromised? Why Companies Aren’t at Risk. Your users’ passwords are the only credentials at risk. In fact, many hackers use employee accounts to gain access to your user database. Learn several ways you can protect your internal accounts with our helpful guide.